Why is Cyber Security Indispensable Now More Than Ever? Top 5 Reasons
Introduction
Nowadays, "cybersecurity" is commonly and frequently heard in every business. The buzz seems to have suddenly developed in the last two years, creating cybersecurity a genuine concern for the companies. With smartphones and other mobile devices' advent, hackers have a much better opportunity to play their cybercrimes.
Statistics reveal that the average ransomware transactions per month are nearly $102.3 million, making cybercrime rates alarming to all businesses. Global connectivity and the increased uses of cloud services to store sensitive information have increased the risks to a more significant extent. While most organizations have initiated taking their necessary precautions against cybercrime threats, some are still taken back because of budget and cost issues.
What Factors are Driving The Hackers?

● Information theft is still one of the highest-paid cybercrimes and is growing significantly. The black hat hackers steal personal information for monetary purposes and sometimes even for fun.
● Some of the hackers hack just for making a point, as in the Ashley Madison Hack.
● Disruption of services and rendering them useless is another planned activity. Personal enmity also becomes a major reason sometimes.
ID Theft Resource Center reveals that there have been 11,762 breaches on record between January 1, 2005, and May 31, 2020. This numeral must have made you realize how significant cybersecurity is.
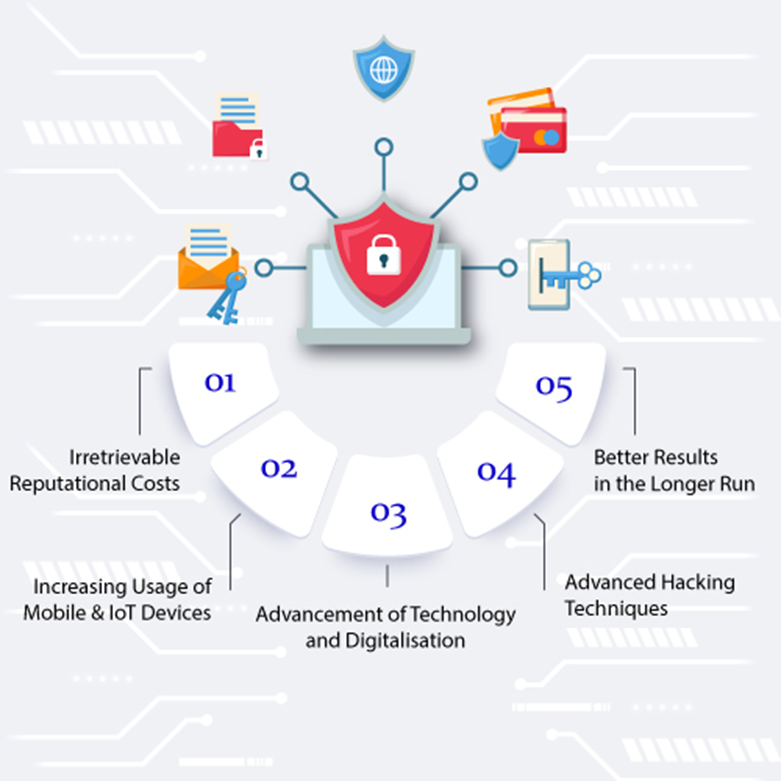
Reasons Why Cybersecurity is Essential Now More Than Ever
Cybersecurity is indeed a hot and intense topic of discussion these days, with the constant advancement of technology. Since data is what drives our lives and gives us identities, we need to protect them and maintain their integrity.
Storing data in our electronic devices and even online is a common practice these days. As a result, cybersecurity has gained more importance and is immensely critical these days.
Irretrievable Reputational Costs
One of the most devastating segments of cybercrimes is information theft. Hackers have improvised their techniques and strategies of data breaches and have become more innovative than ever. These data breaches can include sensitive personal information and sometimes even financial details like credit card numbers, bank account details, and so on.
Their sophisticated methodology remains untraceable by the basic cybersecurity protocols and thus, demands better investments in this field. Information risk management is becoming more significant day by day.
These data leaks vastly taint the reputations of business organizations. Consequently, clients lose their trust in the businesses, and customer retention becomes immensely difficult. Besides, they suffer to get new contracts, and gradually the losses become irretrievable. Disruption to trading is another significant aftereffect as businesses fail to make transactions online.
According to the IBM records, data breach costs increased from $3.86 million to $4.24 million in 2021, the highest average total cost in the last 17 years. The financial damages caused to a company by a cyberattack can be huge. The ease of e-commerce on the dark web will only lead to an increase in the number of such attacks shortly.
Besides economic and reputational losses, the companies can suffer from legal consequences of cyber breaches. All the companies are expected to protect the sensitive information of the staff and customers stored in the system. Suppose the companies fail to protect this personal information, whether deliberately or accidentally, they may be legally accused. They may even need to pay fines and regulatory sanctions.
Increasing Usage of Mobile and IoT Devices
Global Connectivity increases rapidly with the faster adoption of IoT(Internet Of Things) devices. This has unfortunately presented several setbacks. Every mobile, desktop, laptop, or other device connected to the internet can open the gateways of security breaches for malicious hackers to enter into the business. The hackers can now effortlessly find their potential targets and cause permanent damages.
Every business, even the small to medium-sized ones, should adopt proper precautions in cybersecurity to avoid such attacks. Most small-sized businesses ignore these investments thinking they can't be the potential targets for the hackers.
However, the weaker security protocols in these organizations make them more vulnerable and probable targets. The workers in these associations also aren't skilled enough to combat such attacks. Thus, these small businesses suffer devastatingly during cyberattacks, mostly because of the lack of precautions and training. Cyberint claims that nearly 43% of the cyberattacks target small businesses.
American Software developer company SolarWinds suffered from a huge cyberattack in January 2020. The hackers smartly exploited a vulnerability in the company's software and consequently gained access to the administrative details of an account holder. To avoid such cyberattacks, frequent conduction of vulnerability assessments and consequent addressing of the issues is required. Changing the passwords at least once in six months and maintaining backups of all the information is also essential.
The companies should keep all the software up-to-date and install advanced security checks and network settings on the computers. Varonis says only 5% of the companies' folders are properly protected. Creating awareness amongst the employees and training them with the basic preventive and reactive approaches is necessary.
Advancement of Technology and Digitalisation
With passing days, hackers are becoming more sophisticated and highly trained. The gradual adoption of faster broadband service of 5G network has increased the chances of cybercrime threats. NZTech chief Graeme Muller agrees that there is a strong connection between faster networks and rising cybercrimes.
In the present scenario, most businesses are shifting to online stores with well-informed websites being hosted. Until the third quarter of 2020, a total sum of $370.7 million domains registered across all top-level domains. These websites serve as easy entry points to the hackers, making every online business a probable target.
If cybersecurity protocols aren't strictly followed while developing the websites, the businesses become highly vulnerable. Most hackers try to exploit the site visitors, steal the information stored on the websites, and cause reputational losses to the company by hooliganism. Both small and large websites can be potential targets of hackers.
SQL injection attacks have been increasing at an alarming rate in the past few years. The hackers inject malicious codes into the vulnerable SQL queries in these attacks. As a result, the websites return values as desired by the hacker and not what is expected from the websites. These malicious codes are powerful enough to alter the databases and add malicious information to them.
Sometimes, the hackers show unwanted ads and pop-ups and redirect the visitors to scam websites. This leads to a drastic drop in the traffic and impressions of the websites, affecting the companies' sales. Injecting SEO spam on the pages is another everyday activity done by hackers.
Advanced Hacking Techniques
Malware, which refers to malicious software variants, includes viruses, trojans, worms, and spyware. They provide unauthorized access to the computers and may cause permanent damages. Though the employees are often trained with the basic security rules, the hackers tend to find possible ways of a security breach, taking advantage of the recent work from the home scenario and lesser protective clouds.
DDoS (Distributed Denial of Service) attacks are also significantly increasing in recent days. Online business owners must acknowledge themselves with this kind of attack. In these attacks, the targeted business websites are made to slow down by flooding the network, server, or application with fake traffic. Even minute traffic can boost up these attacks, making them major ones.
In February 2020, the cloud computing giant AWS faced a huge DDoS attack through the modernized technique named Connectionless Lightweight Directory Access Protocol (CLDAP) reflection. In this technique, third-party CLDAP servers are being relied upon, and the data sent to the victim is magnificently amplified 56 to 70 times. This attack continued for 3 days and crested at an astounding 2.3 terabytes per second.
Sometimes the hackers write a script that develops multiple permutations and combinations of usernames and passwords. This process continues until the script finds the correct combination for the targeted website. Once the password starts working, they gain access to the admin panel and even to the SFTP server of the websites. They attempt to perform multiple illegal activities, including credit card stealing, spam campaigns, and even coin-miners.
The techniques of hacking are becoming improvised and highly advanced with time. This is making the digital world more exposed to cybercrime threats. We need an equally strong cybersecurity protocol to prevent these attacks and save the companies from the aftereffects.
Better Results in the Longer Run
If you avoid security installations to save your budget, rethink your decision. Cybersecurity is indeed expensive, but the recovery after a cyberattack is much more expensive and sometimes even unaffordable. Not investing your money in cybersecurity is highly risky and may not turn out to be a smart business decision. Reports say that hackers attack a computer in the United States every 39 seconds!
Equifax, the international credit rating agency, faced a serious data breach of nearly $147 million customers. The recovery costs were around $439 million.
Moreover, to create awareness about the necessary investments in cybersecurity, the GDPR(EU General Data Protection Regulation) rules have been introduced. Now, security needs to be considered more seriously than ever. The EU has introduced these rules to ensure that the customers' data is protected by all means. It implies the installation of better technical and organizational measures to protect the consumers' data.
Sometimes, these cyberattacks also lead to loss of jobs and massive unemployment. When a company suffers from cyberattacks, they unemploy several executives as a cost-cutting technique. During these attacks, the hackers sometimes steal the identities of the staff and sell them illegally. This risks the life of the individual and his family. Seldom, the hackers even droop down to the extremes of blackmailing and even extortion.
Every company should train their employees to propagate the importance of cybersecurity and teach them how to deal with cybersecurity threats and reduce them. Cyberint states that 95% of these cyberattacks happen due to human errors.
How Can You Mitigate Cybersecurity Risks in Your Company?

● Keep your system's software updated. The ransomware attacks can be reduced if you have the latest software versions installed in your system. Always keep automated updates turned on. This will help you to get automatic security updates.
● Strong passwords are a must. Use passwords that are easy to remember yet difficult to guess. Make sure to include at least one uppercase letter, lowercase letter, special character, and one digit in your password. Don't keep any public hint to your password, and try to change your password at least once every 6 months. Similarly, create difficult mobile passcodes.
● Phishing scams are increasing every year. One single click on any malicious link can make your data exposed to hackers. Avoid opening emails from suspicious unknown senders. To be extra precautious, you can hover over the link to check where you will be redirected. According to CSO Online, nearly 94% of malware is delivered via email.
● Raise awareness about cybersecurity among the employees. Train them with basic cybersecurity knowledge.
● Biometric Security is another good option. It is significantly difficult to clone or access someone's fingerprint compared to their digital passwords or access cards.
● You should monitor third-party access to your data. Only the trusted business partners and employees should be able to access the company's database.
● Maintain regular backups of the data. In the case of cyber-attacks through ransomware, backups can be your ultimate lifesaver.
● Don't use public wi-fi using a VPN (Virtual Private Network). VPN software can be used to encrypt the traffic between your device and the VPN server.
● Download apps only from trusted sources on your mobiles. Update these apps frequently. Remember that hackers tend to exploit the vulnerabilities of the untouched applications on your devices.
Conclusion
As written above, you must have noticed how catastrophic cyberattacks can be. They can lead to companies' financial, reputational, and legal losses. The aftereffects of a cyberattack are mostly found to be irrecoverable. It is thus highly recommended to make the necessary investments in cybersecurity. Abiding by the few mentioned precautions can make your security risks much lower. It's high time to view cybersecurity as a real concern for any business.
Popular Tags
Recent Posts
Smart automation for cash-strapped startups
The modern data trinity: How medallion architecture, RAG, and data lakes revolutionize enterprise intelligence
Accelerating AI-Driven Development with Docker’s MCP Catalog & Toolkit
Building Intelligent Agent Teams with Google's ADK: A Developer's Guide
We are at